FiberGuide is a Northern Virginia based optical network training and consulting company. Our consulting services include network/service provider support services and connectivity sourcing. We leverage our technical expertise, many years of experience in fiber optics and Information and Communications Technology (ICT) and strong partnerships with key industry players to provide services to the telecommunication and IT industries. Developed by Optical Technology Training (OTT), our optical network training courses include CONA (Certified Optical Network Associate), CONE (Certified Optical Network Engineer) and CFCE (Certified Fiber Characterization Engineer).
FiberGuide Consulting services
We leverage access to hundreds of global carriers to create a one stop source for a wide range of networking solutions. With providers like Verizon Business, Comcast Business, Lumen, GTT, Telia Carrier, NTT and many others, FiberGuide is positioned to be a valuable partner to our clients for such services as dark fiber, VPLS and SD-WAN. On the other hand, we are well positioned to offer valuable services to our network provider partners. We help them deploy and maintain cost efficient networks through network planning, fiber and system specifications, and network testing. Alternatively, we provide the training necessary for our clients’ personnel to more efficiently handle these tasks – as outlined in the following paragraphs.
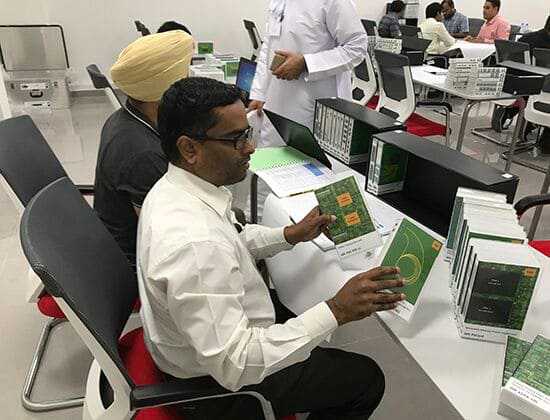
OTT Certified Optical Network Associate (CONA)
The foundation CONA course is specially crafted for optical network planners, project managers, and network operation personnel. It delves into the essential aspects of optical communications, encompassing fiber optics and transmission systems employing direct detection technology. The CONA curriculum extensively covers networks based on single channels or multiple channels such as CWDM, and DWDM. It brings real-world applications like 5G transport, data center interconnects, long-distance networks to the forefront, using case studies during the workshops. Delegates will gain in-depth knowledge about meeting network performance requirements and effectively mitigating fiber impairments such as chromatic dispersion, polarization mode dispersion, and non-linear impairments.
OTT Certified Optical Network Engineer (CONE)
For those looking to elevate their expertise to the next level, FiberGuide offers OTT CONE training. In this advanced optical networking course, delegates go far beyond CONA, where they delve into the transformative power of coherent detection and digital signal processing in optical networking. The program focuses on enabling higher data rates per channel, such as 100Gb/s, 400Gb/s, 800Gb/s, and beyond. Understanding the modifications required for DWDM systems to operate at these advanced data rates is a central theme of the CONE course. Delegates also gain insights into the synergy between optical and electronic technologies that play a pivotal role in overcoming limitations in high-performance optical networks.
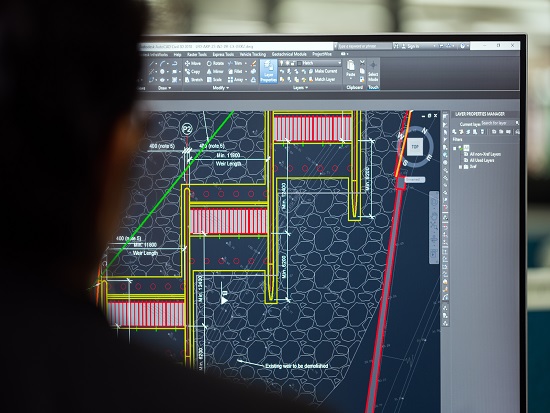
OTT Certified Fiber Characterization Engineer (CFCE)
OTT CFCE or Certified Fiber Characterization Engineer training program is a five-day, intense, hands-on training course. The focus on this course, developed for test engineers, is on developing critical skills required to fully test and verify fiber optic infrastructure that can support high data rate operations of 10Gb/s and above. Delegates learn how to effectively test for key attributes such as spatial losses along a fiber using an OTDR, optical return loss, spectral attenuation, chromatic dispersion, and polarization mode dispersion. Delegates are required to complete a team assignment involving complete characterization of an optical fiber link.